Don't be confused with my other FortiNAC posts where... Full Story
By Manny Fernandez
March 11, 2026
FortiLink NAC or NAC Lite
Don’t be confused with my other FortiNAC posts where we discuss the full blown FortiNAC deployment, discovery, device profiling, etc. In this article we will use a FortiGate and a FortiSwitch. No additional software.
Adding the FortiSwitch
You will need a FortiGate and a FortiSwitch. My configuration is as follows.

I have a ForitGate 120G and a FortiSwitch 110G FPoE. My FortiLink interface was changed from the default of x1 and x2 to Port 15 and Port16.
You want to make sure the switch is stable.

This is before I attached the switch.

When the switch boots up, it will be in an unauthorized state.

Right click on the switch and choose Authorized

The switch rebooted and I subsequently upgraded the switch to the lated OS. Now we can see the switch is Online we are ready to go.
VLANs
When devices are matched by a NAC policy, you can assign those devices to a FortiSwitch NAC VLAN. By default, there are six VLAN templates:
default—This VLAN is assigned to all switch ports when the FortiSwitch unit is first discovered
quarantine—This VLAN contains quarantined traffic
rspan—This VLAN contains RSPAN and ERSPAN mirrored traffic
voice—This VLAN is dedicated for voice devices
video—This VLAN is dedicated for video devices
onboarding—This VLAN is for NAC onboarding devices
You can use the default onboarding VLAN, edit it, or create a new NAC VLAN. If you want to use the default onboarding NAC VLAN, specify it when you configure the FortiSwitch NAC settings. If you want to edit the default onboarding VLAN or create a new NAC VLAN, use the following procedures.
I have created my own VLANs where I will eventually move devices once they are assigned.

I created a the following VLANs
- Corporate – Standard Users
- AP-Mgmt – VLAN for Access Points
- Printer – Obviously
- IT-VLAN – Will Have Mgmt Access (Could be to other switching environments, servers, etc.)
- Isolation – No-Man’s Land. You will be isolated but I will allow you to use DNS and to get to Windows Updates
NAC Policies
By default, you will have the onboarding VLAN in the NAC Policies Section

Lets create our first Policy

In this NAC policy, we are marching Apple devices running macOS and assigning them to the Corporate VLAN.

The next one will be based on Hardware Mfg and Device Family and assign them to the AP-Mgmt VLAN.
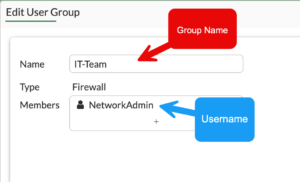
I created a user and added them to a group, but you can use SAML/AD group. Now we will create a policy that will use the credentials.
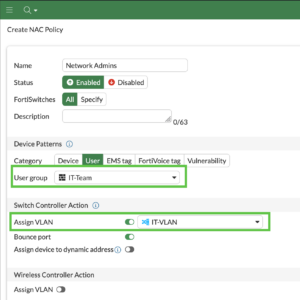
If you are in the IT-Team, you will be moved to the IT-VLAN

This policy is based on High and Critical Vulnerabilities and added to isolations

Here are all the policies we created earlier.
Firewall Policies

Here we can see where IT can have access to everything, while Isolation VLAN can get to Google and L3 DNS resolvers and Windows Updates sites.
Port Configuration
In order to NAC’afi (i think I made up this word) you sill need to tell the FortiGate and specifically, the FortiSwitch you will need to change the port mode from static to NAC

You can see that the moment you do that, the Native VLAN will change to the Onboarding VLAN.
Validation
You can go to Dashboard then Assets & Identities and choose the Matched Devices widget. You should see your test PC connected.

You can see that it matched my Windows NAC Policy and that the Assigned VLAN is Corporate.
Recent posts
-

-

This is the third session in a multi-part article... Full Story
-

Today I was configuring key-based authentication on a FortiGate... Full Story
-

Netcat, often called the "Swiss Army knife" of networking,... Full Story
-

At its core, IEEE 802.1X is a network layer... Full Story
-

In case you did not see the previous FortiNAC... Full Story
-

This is our 5th session where we are going... Full Story
-

Now that we have Wireshark installed and somewhat configured,... Full Story
-

The Philosophy of Packet Analysis Troubleshooting isn't about looking... Full Story
