Part of my daily gig is creating BoMs (Bill-of-Materials)... Full Story
By Manny Fernandez
March 17, 2026

Monkey Bites – ICMP Security Risks
ICMP introduces several security risks, but careful filtering, rate limiting, and monitoring can keep it usable for diagnostics without exposing your network unnecessarily.
Key ICMP Security Risks
Lack of authentication and spoofing
ICMP has no built‑in authentication, so attackers can forge source addresses and send fake error or control messages (like redirects), enabling man‑in‑the‑middle or traffic black‑holing attacks.
ICMP flood (ping flood) and DDoS
Attackers overwhelm a target with large volumes of ICMP Echo Requests, consuming bandwidth and CPU and causing denial of service; this is one of the most common ICMP‑based DDoS vectors.
Smurf and broadcast amplification
In a Smurf attack, the attacker sends ICMP Echo Requests to broadcast addresses with the victim spoofed as the source, causing many hosts to reply to the victim and amplifying the traffic.
Ping of Death and malformed packets
Historically, oversized or malformed ICMP packets could trigger buffer overflows and crashes in vulnerable systems; modern stacks are mostly patched, but similar logic‑bug exploitation remains a risk.
ICMP redirect abuse
Forged ICMP Redirect messages can convince hosts to send traffic via an attacker‑controlled router, enabling interception or modification of traffic.
Reconnaissance and mapping
Attackers use ICMP echo and time‑exceeded responses (ping, traceroute) to map live hosts, network topology, and filtering behavior for later attacks.
Mitigation at Network Perimeter
Restrictive, type‑aware firewall rules
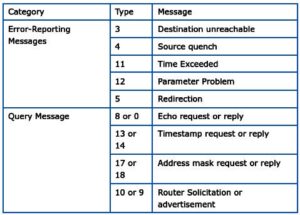
Allow only necessary ICMP types (e.g., Destination Unreachable, Time Exceeded) while blocking or tightly controlling Echo Requests from untrusted networks.
Rate limiting ICMP
Configure routers and firewalls to limit ICMP packets per source or per interface, which reduces the impact of floods while still permitting legitimate diagnostics.
Block broadcast and directed‑broadcast ICMP
Disable IP‑directed broadcasts and block ICMP to broadcast addresses to eliminate Smurf‑style amplification.
Filter and log at DDoS edges
Use upstream DDoS protection to detect ICMP flood patterns and scrub malicious traffic before it reaches your network edge.
Mitigation Inside the Network
Network segmentation and access control
Use VLANs and internal ACLs so that only necessary segments can exchange ICMP, limiting lateral movement and internal flood impact.
Careful handling of ICMP redirects
Most enterprise deployments disable ICMP Redirect acceptance on servers and critical hosts, relying instead on proper routing configuration.
Secure host configurations
Ensure OSes are patched against historical ICMP bugs and configure host firewalls to respond to ICMP only as required for operations.
Monitoring and Operational Best Practices
Traffic baselining and anomaly detection
Establish normal ICMP volume and patterns, then alert on sudden spikes or unusual types that may indicate reconnaissance or an attack.
Intrusion detection/prevention systems (IDS/IPS)
Use IDS/IPS signatures to detect ICMP floods, Smurf attempts, or suspicious redirect and unreachable patterns, and automatically block or rate‑limit offenders.
Selective, not blanket, blocking
Completely disabling ICMP breaks PMTUD and complicates troubleshooting; experts recommend keeping critical error types (like fragmentation needed) while controlling echo and unnecessary types.
Example Policy Balance
– Allow ICMP Destination Unreachable and Time Exceeded from anywhere, possibly with rate limits, to preserve path MTU discovery and diagnostics.
– Allow Echo Requests only from internal or trusted monitoring systems; rate‑limit any externally visible echo responses.
– Block ICMP redirects at hosts and edge devices, and disable directed broadcasts to eliminate common abuse paths.
If you can, try to be explicit about the ICMP traffic.
Recent posts
-

-

ICMP introduces several security risks, but careful filtering, rate... Full Story
-

The command diag debug application dhcps -1 enables full... Full Story
-

In the world of FortiOS, execute tac report is... Full Story
-

LLDP; What is it The Link Layer Discovery Protocol... Full Story
-

What it actually does When you run diagnose fdsm... Full Story
-

Monkey Bites are bite-sized, high-impact security insights designed for... Full Story
-

I have run macOS in macOS with Parallels but... Full Story
-

Don't be confused with my other FortiNAC posts where... Full Story
-

This is the third session in a multi-part article... Full Story
-

Today I was configuring key-based authentication on a FortiGate... Full Story
-

Netcat, often called the "Swiss Army knife" of networking,... Full Story
-

At its core, IEEE 802.1X is a network layer... Full Story
-

In case you did not see the previous FortiNAC... Full Story
-

This is our 5th session where we are going... Full Story
-

Now that we have Wireshark installed and somewhat configured,... Full Story
-

The Philosophy of Packet Analysis Troubleshooting isn't about looking... Full Story
