If you've spent any time configuring user authentication on... Full Story
By Manny Fernandez
April 7, 2019

Using NMAP
On September 1, 1997, Nmap was first released in Phrack magazine Issue 51, Article 11. Since then it has been used by black hats, white hats and everyone in between. It is a super useful tool and I can tell you that being in the role I am in today, I do not use it as much as I used to but even still, I use it at least 5 times a week. In this post, I will try to touch on the basics and maybe some advanced uses for nmap.
Nmap works on the most major operating systems. From their website, this is what they say:
Linux (all distributions)
Microsoft Windows
Mac OS X
FreeBSD, OpenBSD, and NetBSD
Sun Solaris
Amiga, HP-UX, and Other Platforms
I will be running this from a Linux VM and it happens to be running :
[root@observium ~]# nmap -version
Nmap version 6.40 ( http://nmap.org )
Platform: x86_64-redhat-linux-gnu
Compiled with: nmap-liblua-5.2.2 openssl-1.0.1e libpcre-8.32 libpcap-1.5.3 nmap-libdnet-1.12 ipv6
Compiled without:
Available nsock engines: epoll poll select
Target Selection
In this section, you can see the various types of switches you can use to get the results you are looking for from a target selection perspective.
Other options, are the iR which chooses random IPs
nmap -iR 10 10.1.106.0/24
Nmap done: 11 IP addresses (1 host up) scanned in 7.98 seconds
nmap -iR 10 10.1.106.0/24
Nmap done: 16 IP addresses (6 hosts up) scanned in 36.22 seconds
Specifying Ports
Types of Scan
Operating System and Service Detection Type
Saving Results to a File
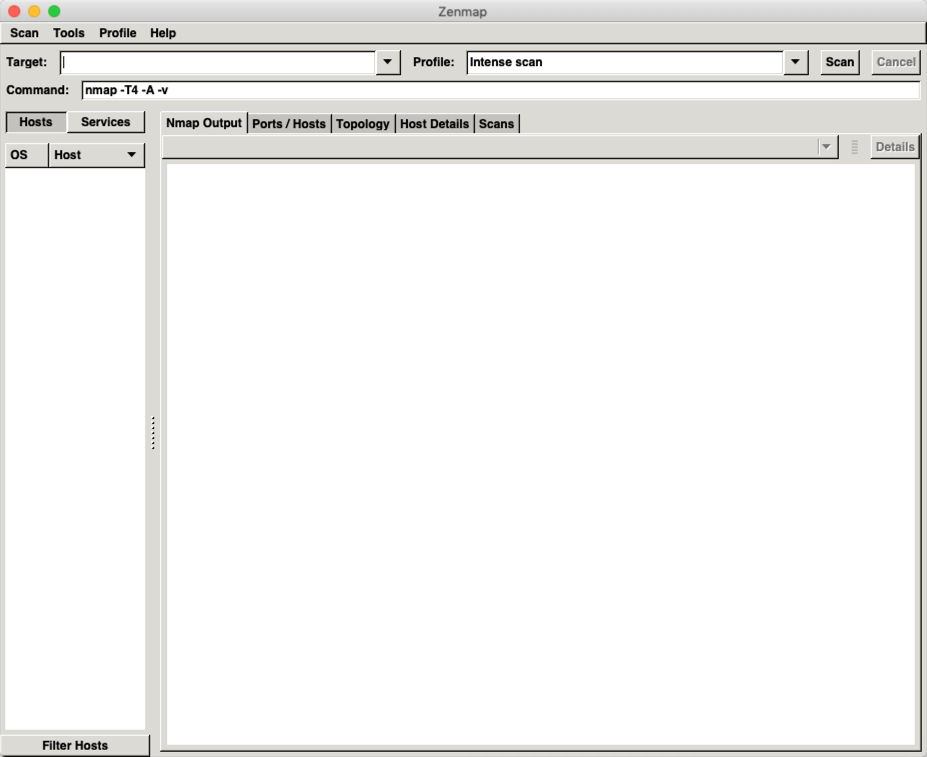
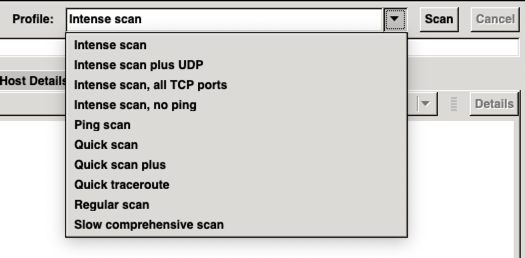
GUI Version
Recent posts
-

-

DNS is one of those technologies that quietly underpins... Full Story
-

BGP issues on FortiGate firewalls usually trace back to... Full Story
-

Every time your laptop talks to your router, a... Full Story
-

If you've spent any time configuring NAT on a... Full Story
-

If you have spent any time configuring firewall policies... Full Story
-

High availability on FortiGate is one of those features... Full Story
-

If you've configured SD-WAN on a FortiGate, you've almost... Full Story
-

FortiLink is the management protocol that turns a FortiSwitch... Full Story
-

FortiSwitches are pretty rock solid from Mean Time Between... Full Story
-

This is a quicky tip. Have you ever gone... Full Story
-

DNS is one of those quiet pieces of internet... Full Story
-

This article is an updated version of the previous... Full Story
-

You will add ns2 as a secondary (slave) BIND9... Full Story
-

In the process of deploying my lab, I needed... Full Story
-

RFC 8805, used to be known as Self-Correcting IP... Full Story
-

Years back, I wrote an article about certificate pinning. ... Full Story
-

FortiGates have the ability to send alerts to Microsoft... Full Story
-

In this post, I am going to walk through... Full Story
-

Troubleshooting VoIP on a FortiGate can feel like trying... Full Story
-

Prior to FortiOS 7.0, there were three commands to... Full Story
-

In this post, I am going to go over... Full Story
-

What we are going to do: We are going... Full Story
-

Choosing between FGCP (FortiGate Clustering Protocol) and FGSP (FortiGate... Full Story
-

Creating a VLAN on macOS (The "Pro" Move) A... Full Story
-

This blog post explores the logic behind how macOS... Full Story
-

Pretty Fly for a Wi-Fi Tell My Wi-Fi Love... Full Story
-

Part of my daily gig is creating BoMs (Bill-of-Materials)... Full Story
-

ICMP introduces several security risks, but careful filtering, rate... Full Story
-

The command diag debug application dhcps -1 enables full... Full Story
-

In the world of FortiOS, execute tac report is... Full Story
-

LLDP; What is it The Link Layer Discovery Protocol... Full Story
-

What it actually does When you run diagnose fdsm... Full Story
-

Monkey Bites are bite-sized, high-impact security insights designed for... Full Story
-

I have run macOS in macOS with Parallels but... Full Story
-

Don't be confused with my other FortiNAC posts where... Full Story
-

This is the third session in a multi-part article... Full Story
-

Today I was configuring key-based authentication on a FortiGate... Full Story
-

Netcat, often called the "Swiss Army knife" of networking,... Full Story
-

At its core, IEEE 802.1X is a network layer... Full Story
-

In case you did not see the previous FortiNAC... Full Story
-

This is our 5th session where we are going... Full Story
-

Now that we have Wireshark installed and somewhat configured,... Full Story
-

The Philosophy of Packet Analysis Troubleshooting isn't about looking... Full Story
-

Overview FortiOS 8.0 introduces custom tags as a first-class... Full Story
-

These are two distinct mechanisms on FortiOS, and conflating... Full Story
-

Replacement messages are the pages and text blocks that... Full Story
