If you've spent any time configuring user authentication on... Full Story
By Manny Fernandez
February 22, 2021

FortiGate AD Polling with Windows Server 2003
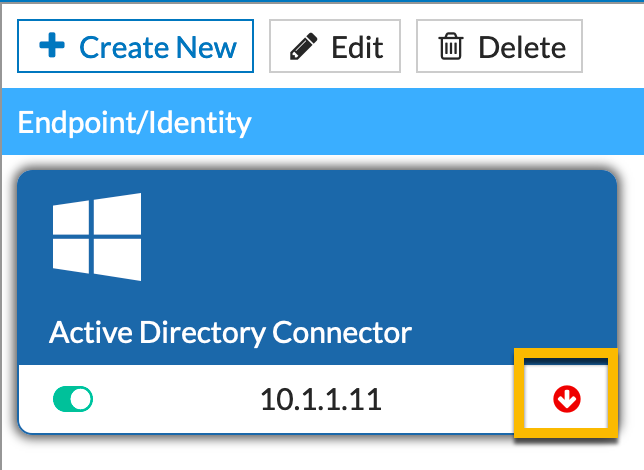
Today, I was helping a customer set up Active Directory polling from a FortiGate firewall using the External Connector which is included in 6.2 and above. With this feature, you are able to poll active directory users directory from a Windows Domain Server. However this was failing and customer could not figure out why it was not working. It took a little bit to figure out but here is what I found.
I will start by telling you what I found. The customer was running Windows Server 2003. I know, that is crazy, but it is what the customer was running.
After setting up the external connector we were getting the following:
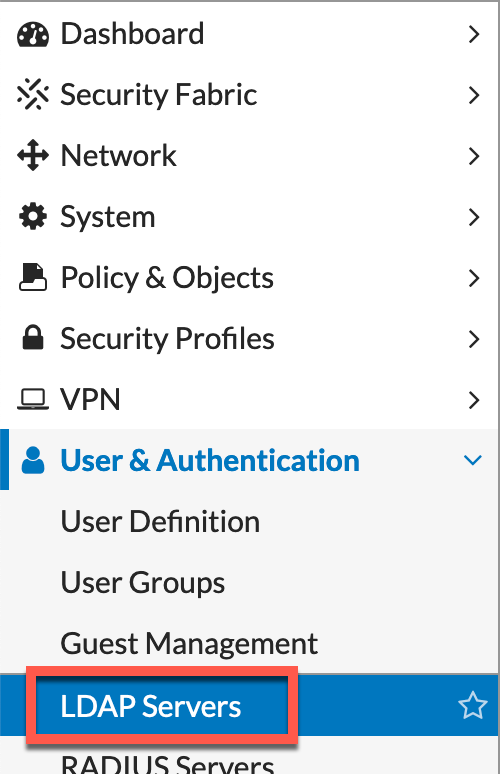
We validated that the LDAP Server under the User & Authentication
To begin, we started with some basic dia debug commands to see what was going on.
diag debug application fssod -1
The output was as follows:
[client_pkt_process:794] Received heartbeat
[handle_reply:491] wrong format of data status. len 8 <> 4.
[handle_reply:491] wrong format of data status. len 8 <> 4.
[handle_reply:491] wrong format of data status. len 8 <> 4.
[handle_reply:491] wrong format of data status. len 8 <> 4.
[handle_reply:491] wrong format of data status. len 8 <> 4.
[handle_reply:491] wrong format of data status. len 8 <> 4.
Next step was to get a packet capture from the FortiGate to see what was going on.
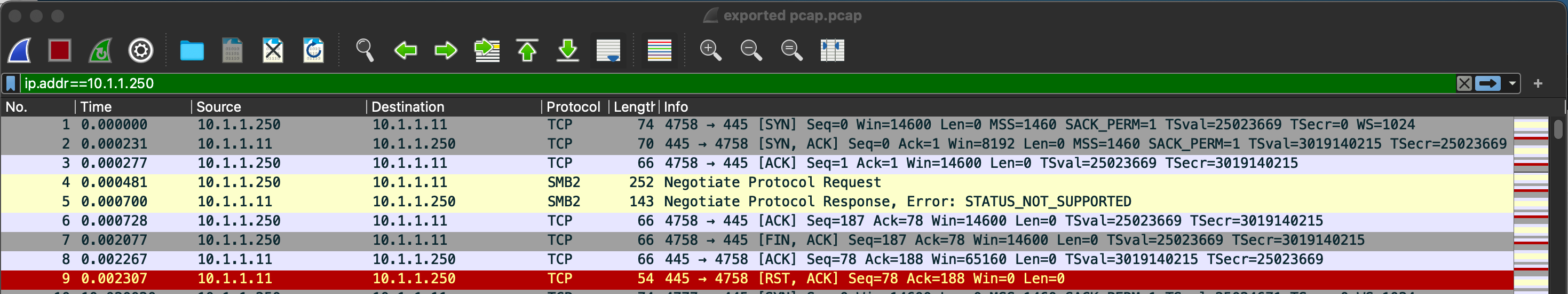
As you can see in the screenshot above, we can see packets 4 & 5 are the SMBv2 connection the FortiGate is trying with. We can see the STATUS_NOT_SUPPORTED. This is what gave me a huge clue.
I then went back to the FortiGate CLI and ran an additional debug command
diag debug application smbcd -1
Here is the output
PULM-FW-01 # smbcd: smbcd_process_request:981 got cmd id: 6
smbcd: smbcd_process_request:994 got rpc log field.
smbcd: smbcd_process_request:1006 got rpc username: administrator@<REMOVED>.local
smbcd: smbcd_process_request:1012 got rpc password: XXXXXXXX
smbcd: smbcd_process_request:1016 got rpc port: 0
smbcd: smbcd_process_request:1022 got rpc logsrc: security
smbcd: smbcd_process_request:1000 got rpc server: 10.1.1.11
smbcd: smbcd_process_request:1049 got VFID, 0
smbcd: smbcd_process_request:1182 got rpc eventlog read command
smbcd: rpccli_eventlog_open:121 /code/FortiOS/fortinet/daemon/smbcd/smbcd_eventlog.c-121: connect err(NT_STATUS_NOT_SUPPORTED)
smbcd: rpc_cmd_eventlog_read:930 open rpc err(10.1.1.11:administrator@<REMOVED>.local:0) from security log!, Please check correct server name, user name, password, port and log
source
This did it for me. I wanted to see what version of SMB the server was running.
I RDP’d to the server and launched the Powershell console. I tried running the Get command from the powershell but since it was an older Windows Server, it did not work
Get-SmbConnection
So I went to Google and found the following command
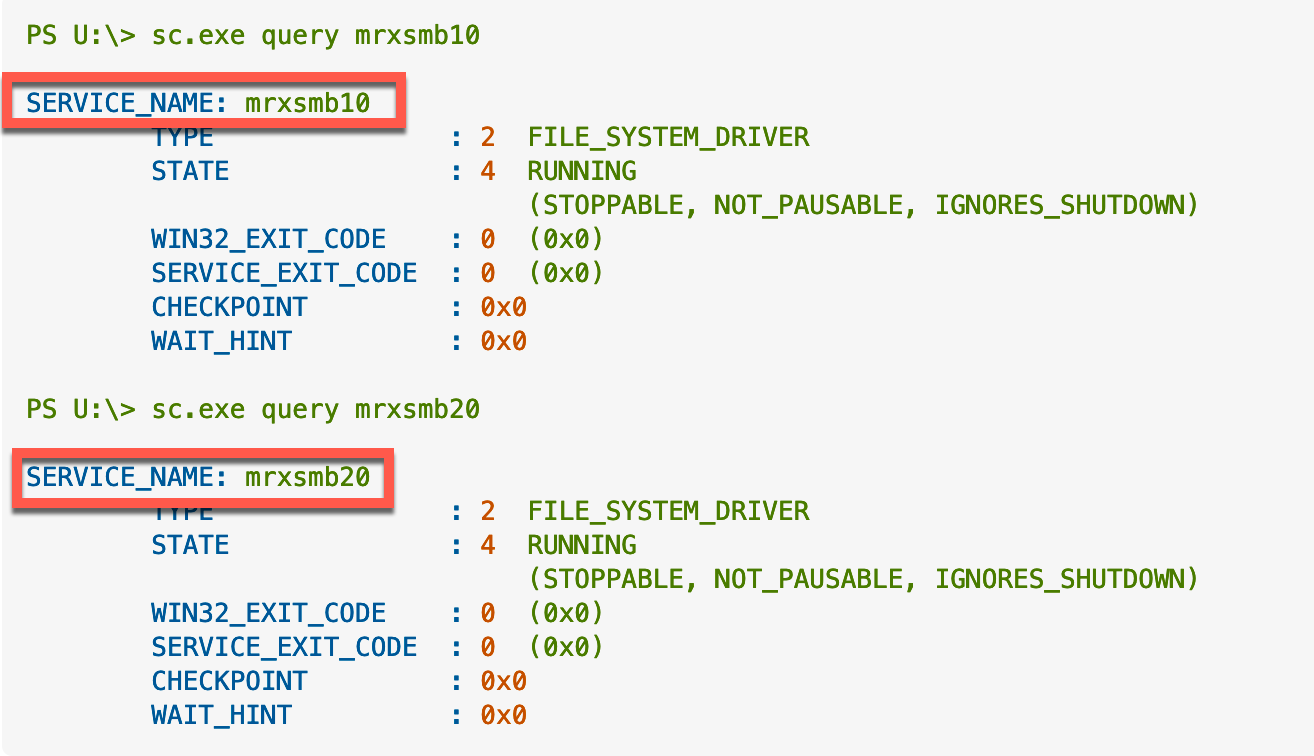
sc.exe
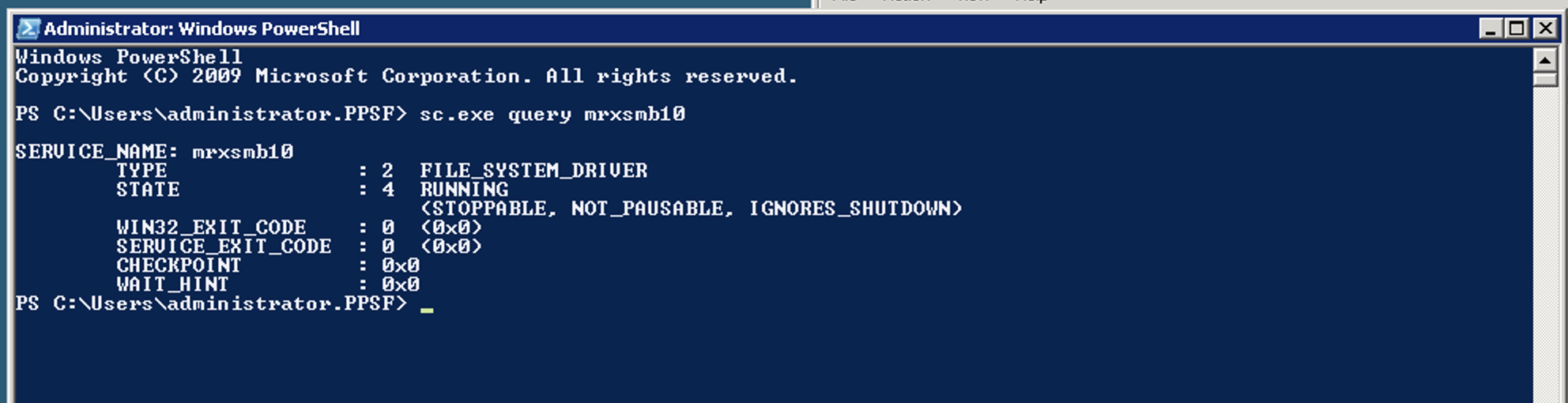
As you can see in the screenshot, we can see that we are running SMBv1 (mrxsmb01). When querying for v2, it fails.
This is how v1 and v2 looks
After upgrading the DC to 2019, the problem went away.
Hope this helps.
Recent posts
-

-

DNS is one of those technologies that quietly underpins... Full Story
-

BGP issues on FortiGate firewalls usually trace back to... Full Story
-

Every time your laptop talks to your router, a... Full Story
-

If you've spent any time configuring NAT on a... Full Story
-

If you have spent any time configuring firewall policies... Full Story
-

High availability on FortiGate is one of those features... Full Story
-

If you've configured SD-WAN on a FortiGate, you've almost... Full Story
-

FortiLink is the management protocol that turns a FortiSwitch... Full Story
-

FortiSwitches are pretty rock solid from Mean Time Between... Full Story
-

This is a quicky tip. Have you ever gone... Full Story
-

DNS is one of those quiet pieces of internet... Full Story
-

This article is an updated version of the previous... Full Story
-

You will add ns2 as a secondary (slave) BIND9... Full Story
-

In the process of deploying my lab, I needed... Full Story
-

RFC 8805, used to be known as Self-Correcting IP... Full Story
-

Years back, I wrote an article about certificate pinning. ... Full Story
-

FortiGates have the ability to send alerts to Microsoft... Full Story
-

In this post, I am going to walk through... Full Story
-

Troubleshooting VoIP on a FortiGate can feel like trying... Full Story
-

Prior to FortiOS 7.0, there were three commands to... Full Story
-

In this post, I am going to go over... Full Story
-

What we are going to do: We are going... Full Story
-

Choosing between FGCP (FortiGate Clustering Protocol) and FGSP (FortiGate... Full Story
-

Creating a VLAN on macOS (The "Pro" Move) A... Full Story
-

This blog post explores the logic behind how macOS... Full Story
-

Pretty Fly for a Wi-Fi Tell My Wi-Fi Love... Full Story
-

Part of my daily gig is creating BoMs (Bill-of-Materials)... Full Story
-

ICMP introduces several security risks, but careful filtering, rate... Full Story
-

The command diag debug application dhcps -1 enables full... Full Story
-

In the world of FortiOS, execute tac report is... Full Story
-

LLDP; What is it The Link Layer Discovery Protocol... Full Story
-

What it actually does When you run diagnose fdsm... Full Story
-

Monkey Bites are bite-sized, high-impact security insights designed for... Full Story
-

I have run macOS in macOS with Parallels but... Full Story
-

Don't be confused with my other FortiNAC posts where... Full Story
-

This is the third session in a multi-part article... Full Story
-

Today I was configuring key-based authentication on a FortiGate... Full Story
-

Netcat, often called the "Swiss Army knife" of networking,... Full Story
-

At its core, IEEE 802.1X is a network layer... Full Story
-

In case you did not see the previous FortiNAC... Full Story
-

This is our 5th session where we are going... Full Story
-

Now that we have Wireshark installed and somewhat configured,... Full Story
-

The Philosophy of Packet Analysis Troubleshooting isn't about looking... Full Story
-

Overview FortiOS 8.0 introduces custom tags as a first-class... Full Story
-

These are two distinct mechanisms on FortiOS, and conflating... Full Story
-

Replacement messages are the pages and text blocks that... Full Story
